Database Scanning with cPGuard
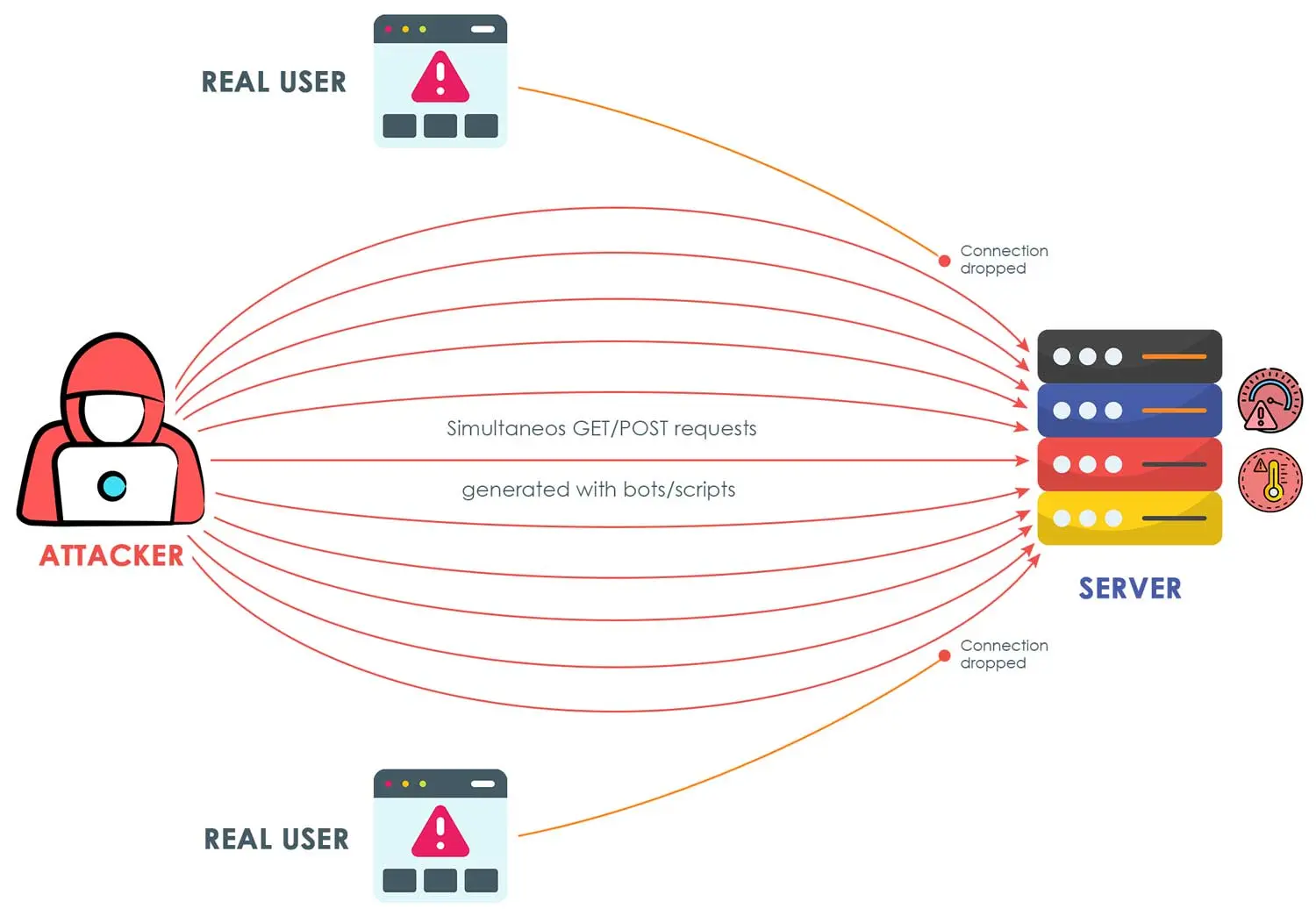
Website infections are no longer limited to just files — increasingly, attackers are targeting databases as well. Once a vulnerability is discovered, malicious actors can inject harmful code directly into the database. This can result in Redirection of visitors to compromised websites, Injection of JavaScript into the visitor’s browser and various other malicious activities
These types of infections are especially dangerous as they can compromise site functionality, user trust, and reputation, and may lead to your website being blacklisted by antivirus and security solutions.
Introducing the WordPress Database Scanner
At cPGuard, we’ve observed that WordPress websites are most commonly affected by database-based code injections. To address this, we’ve introduced a new Database Scanner module as part of our security suite.
This module is carefully designed to:
- Minimize resource usage
- Avoid false positives
- Continuously improve through pattern-based detection
- Auto-update its threat detection patterns
How the Database Scanner Works
The database scanner functions as an extension to our CMS Scanner and Threat Finder. It is triggered under the following scenarios:
1. Manual Scan
When a manual scan is initiated, cPGuard automatically checks if the scan path contains a valid WordPress installation. If found, the database scan is run automatically and appended to the full scan report. The result is also available at Virus Scanner → DB Scanner
2. Scheduled Scanning
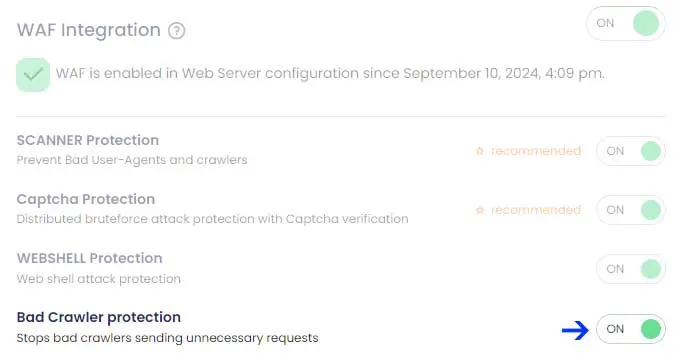
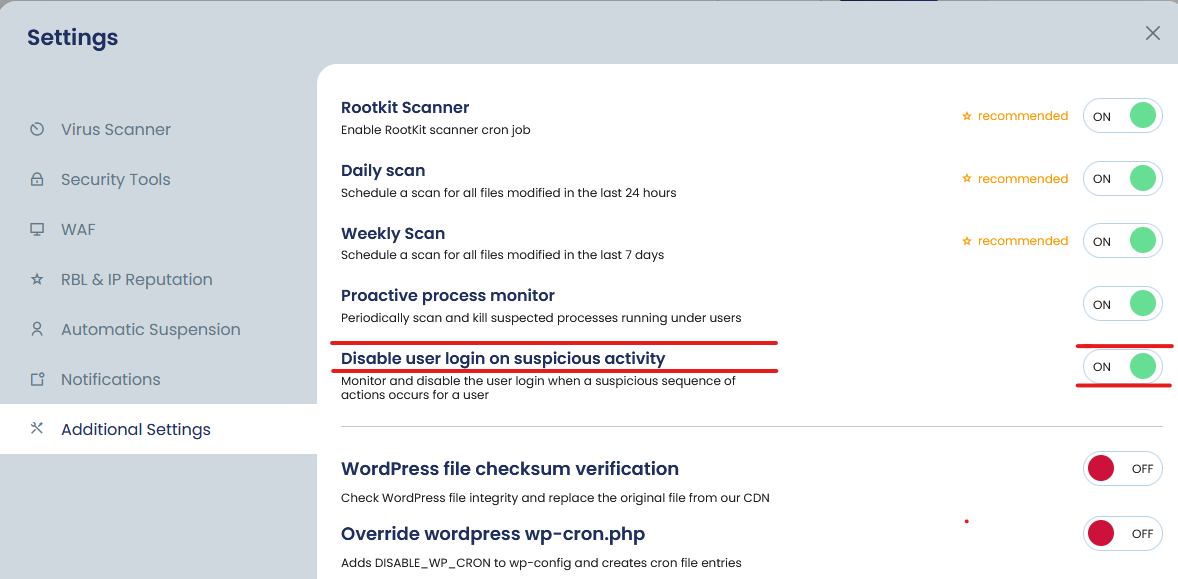
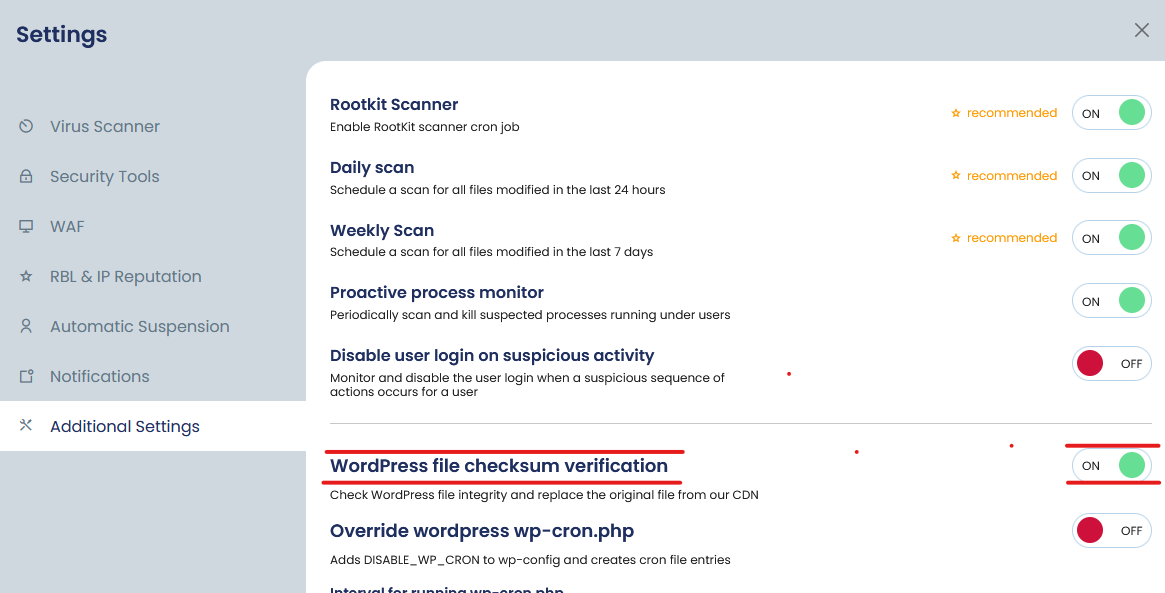
We run daily CMS discovery and analysis across your server. You can enable automatic database scans by toggling the feature under:
App Portal → Server → Settings → Virus Scanner → Database Scanner
Once enabled, the database will be scanned daily, and the results will appear under:
Virus Scanner → DB Scanner
3. Command-Line Interface (CLI)
You can run a database scan directly via the command line using the cpgcli utility.
Scan a specific WordPress installation:
cpgcli dbscan --scan /path/to/wp-installationScan all WordPress databases on the server:
cpgcli dbscan --scan --allFor full usage instructions:
cpgcli dbscan --helpNote: CLI-based scans display results directly in the console and do not store logs.
Roadmap & Future Enhancements
This database scanner is built on a robust foundation that allows for continued improvements. While the current version supports WordPress, We are actively working on adding more signature, Improving performance and extending support to other CMS platforms in future releases.
Stay tuned for updates, and as always, your feedback is welcome as we strive to make cPGuard the most comprehensive and efficient security solution for your web hosting environment.