Announcing cPGuard Firewall 5.83.00: Enhanced Performance with iptables & New Features
We are excited to announce a major update to the cPGuard system firewall. Since our initial NFT-based launch in late 2025, we have been listening closely to your feedback and monitoring performance across diverse environments.
In version 5.83.00, we are introducing a revamped firewall architecture designed for stability, speed, and better user control.
The Shift: Returning to iptables/ipset
When we first introduced the NFT-based firewall, the goal was to leverage modern netfilter tools for a lighter, faster experience. However, real-world deployments presented unexpected challenges, including:
- Stalled firewall rules and slow rule checks.
- Unexpected rule failures.
- Performance bottlenecks under heavy loads.
After extensive internal testing and consultation with our customers, we have decided to revamp the system using iptables/ipset as the primary provider. This ensures the reliability you expect from cPGuard, while still keeping nftables available as an option for those who prefer it.
What’s New in Version 5.83.00?
The latest version is more than just a provider shift; it includes several functional enhancements:
- Optimized Performance: The iptables-based system is significantly faster and maintains a low system load, even when managing tens of thousands of IP addresses.
- Advanced DoS Mitigation: New rules allow you to set connection limits per port/IP. The updated logic also resolves excessive logging issues during active attacks.
- IP & Country Ignore Lists: Entries in the ignore list will now bypass deny rules and the IPDB, ensuring your trusted connections are never interrupted.
- Flexible Providers: While iptables is now the default for new installations, you can switch between iptables and nftables at any time via the UI or CLI.
Introducing the New Grey List & Captcha Unlock
To reduce support tickets and improve the end-user experience, we’ve introduced a 24-hour Grey List.
If an IP is temporarily blocked, users can now use a Captcha-based unlock option to delist themselves (similar to CSF messenger).
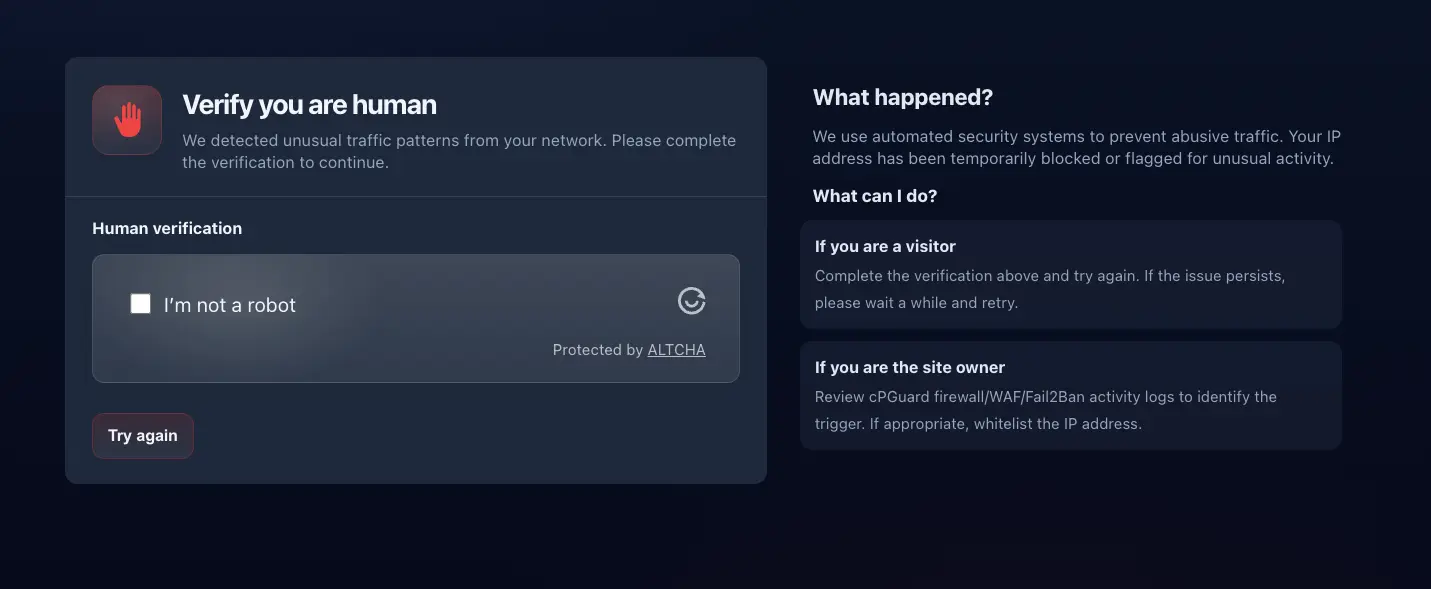
Note: Currently available for cPanel and DirectAdmin, with support for more panels coming soon.
How to Switch to the iptables Firewall
To ensure stability, we are not enforcing the new iptables ruleset on existing installations automatically. If you wish to migrate your current server to the new firewall, you can do so via:
- Command Line Interface (CLI): Run the following command: cpgcli fw –provider iptables
- App Portal: Navigate to Protection > Firewall and update your settings.
Looking Ahead: The New LFD Module
Our work doesn’t stop here. We are currently developing a new LFD (Log Failure Daemon) module to replace the existing Fail2ban-based monitoring. This new system will be:
- Lighter and Faster: Built specifically for the cPGuard ecosystem.
- Tightly Integrated: Allowing the Grey List to be fully utilized so genuine clients can easily unlock themselves after a block.
Stay tuned for these upcoming changes as we continue to evolve cPGuard to meet your security needs!

